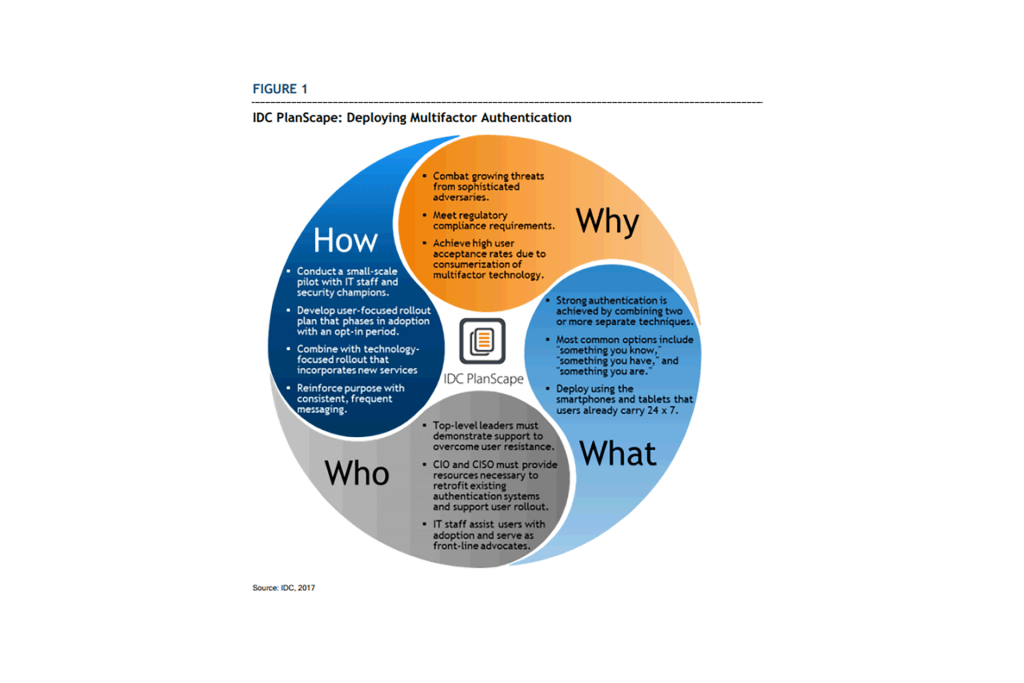
MFA, Deploying Multifactor Authentication
Deploying Multifactor Authentication (MFA) EXECUTIVE SUMMARY Multifactor authentication (MFA) provides organizations with an effective security control that overcomes the weaknesses of knowledge-based authentication and protects network, application, and data assets in an increasingly sophisticated threat environment. By combining passwords with physical devices and/or biometric measurements, organizations add a layer of strong security and protect themselves against password theft. Recent advances in multifactor authentication make this technology more accessible to nontechnical end users and allow widespread deployment throughout the organization. Using multifactor authentication may now be as simple as clicking a button on a pop-up window that appears on the smartphone that a user was already carrying. The simplicity of this …